Cloud Access Security Broker (CASB) Definition
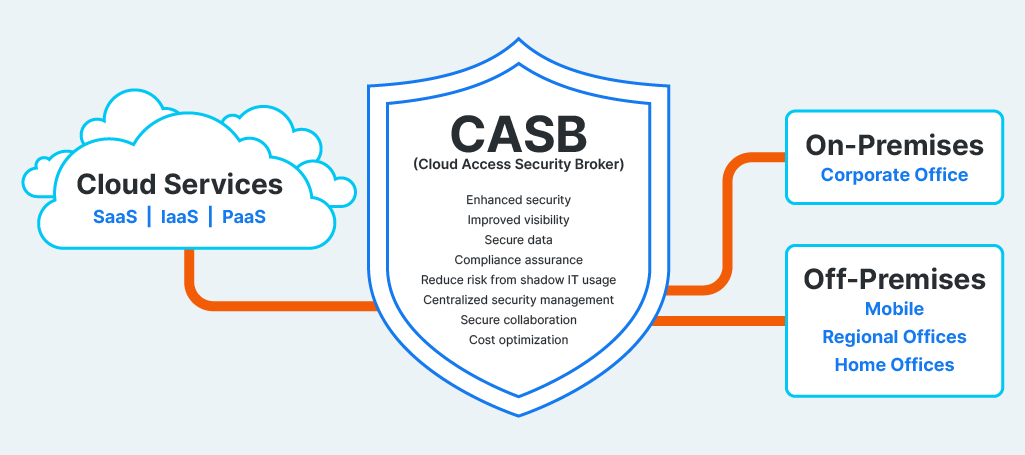
A cloud access security broker (CASB) sits between cloud application providers and users, offering visibility and control over cloud data, usage, access, and security.
CASBs typically offer encryption, access control, threat protection, and monitoring, helping organizations enforce security policies and ensure compliance. This aids in protecting sensitive data as it moves between on-premises devices and multiple cloud environments.
CASB FAQs
What is CASB?
CASB security protects data, applications, and users in cloud environments.
What are the 4 Pillars of CASBs?
- Visibility: Visibility and control over user activities
- Compliance: Strict enforcement of security policies to ensure compliance
- Data security: Protection of data between devices and in cloud environments
- Threat protection: Identification and response to potential threats in cloud environments
Key aspects of CASB technology typically include:
- Governing cloud usage with real-time monitoring
- Offering data protection and network security services with tokenization, encryption, or upload prevention
- Multi-factor authentication (MFA), single sign-on (SSO), and session management
- Cloud services focused on prevention of phishing attacks, insider threats, data breaches, malware detection, and security policy enforcement
What Does a CASB Do?
A CASB creates a more user-friendly, consistent, and secure method for applications users and developers to access cloud resources. For the app developer, the CASB works to ensure compliance and prevent breaches and downtime.
Top CASB use cases include:
- Compliance enforcement. CASBs help organizations achieve data privacy compliance with regulations such as GDPR, HIPAA, and PCI DSS.
- Activity monitoring. CASBs make user activities, data transactions, and configuration changes in cloud applications visible so organizations can detect suspicious behavior, audit usage patterns, and investigate security incidents.
- Access control and CASB authentication. CASBs regulate user access to cloud resources via MFA, SSO, and session management.
- Data protection. CASBs enforce encryption, tokenization, and data loss prevention (DLP) policies.
- Shadow IT discovery. CASB features help organizations assess the extent of shadow IT usage by monitoring network traffic and analyzing cloud service usage patterns.
- Threat detection and response. CASB behavior analytics, anomaly detection, and threat intelligence capabilities allow organizations to respond to malicious activities and security breaches in cloud environments.
- Cloud security posture management (CSPM). CASBs help identify misconfigurations, security gaps, and compliance violations in cloud infrastructure and recommend remediations.
- Data governance and control. CASB capabilities help implement granular data governance policies and controls for cloud applications and enforce policies for data access, sharing, and usage so data is handled in line with organizational policies and regulatory requirements.
- Secure collaboration. CASBs offer secure sharing mechanisms for cloud-based collaboration tools such as file-sharing applications and productivity suites.
- API integration. Seamless integration with cloud APIs offers real-time visibility, data protection, and control over cloud resources.
- Incident response. CASBs offer orchestration tools, forensic analysis, and a means for investigating security incidents and data breaches in cloud environments.
Components of CASB Architecture
In addition to the tools mentioned above, CASB architecture typically consists of components that collectively secure and control cloud environments:
Policy engine. This core CASB architecture component defines, enforces, and manages security policies, allowing administrators to create granular policies based on user roles, device types, location, data sensitivity, and other factors.
Integration APIs. These facilitate integration with existing security infrastructure and tools, such as SIEM systems, identity providers, and endpoint security solutions.
Some aspects of CASB architecture are specific to the deployment model of the CASB solution—proxy-based, API-based, or agent-based:
Proxy/gateways. These serve as intermediaries between users/devices and cloud applications in proxy-based CASB architectures. Proxies and gateways intercept and inspect traffic between users and cloud services, enforcing security policies, and applying controls such as encryption, DLP, and access controls.
API connectors. These integrate with cloud service provider APIs to gain visibility into cloud usage, data, and activities in API-based CASB architectures. They collect metadata and logs from cloud applications, enabling CASBs to monitor and control cloud usage without intercepting network traffic.
Lightweight software agents. These are deployed on endpoints (e.g., laptops, mobile devices) to monitor and secure interactions with cloud applications in agent-based CASB architectures to provide visibility into cloud usage, enforce security policies, and apply controls locally.
CASB Benefits
There are several benefits of CASBs for organizations adopting cloud applications and services:
- Enhanced security. CASB solutions provide advanced security controls and policies that protect data, applications, and users in cloud environments and mitigate security risks.
- Improved visibility and tighter access control. High visibility into sanctioned and unsanctioned applications, user activities, and data transactions allows organizations to control cloud usage, enforce security policies, and ensure compliance.
- Secure data. CASBs help organizations protect sensitive data stored or transmitted in the cloud to stay confidential, even when accessed from multiple devices and locations.
- Compliance assurance. CASB compliance tools assist with data residency requirements and audit trails under regulations such as GDPR, HIPAA, and PCI DSS.
- Reduce risk from shadow IT usage. CASBs enable organizations to discover and assess shadow IT use including unauthorized cloud applications and services, allowing users to mitigate associated risks.
- Centralized security management. CASBs provide a single platform for managing security policies and controls across multiple cloud applications and services within an organizational cloud environment.
- Secure collaboration. CASBs facilitate secure cloud-based collaboration to ensure that sensitive information is protected.
- Cost optimization. CASBs help identify underutilized resources, detecting unauthorized cloud usage, and enforcing cost-saving policies.
CASB Best Practices
There are several CASB guidelines and best practices for organizations to consider:
- Assess cloud risks. Organizations should conduct comprehensive CASB assessments to identify security threats and compliance risks and requirements associated with their cloud environment and its sensitive data.
- Define security policies. Establish clear, comprehensive cloud usage security policies that align with organizational goals, regulatory requirements, and industry best practices.
- Understand CASB performance capabilities. Each solution has its own capabilities and features; be aware of how each of the organization’s implemented CASB controls integrates with existing security infrastructure, how each one is deployed (proxy-based, API-based, agent-based), and how it addresses specific security and compliance requirements.
- Implement least privilege access. Restrict user access to cloud resources based on roles and responsibilities. Implement granular access controls and strong authentication.
- Encrypt sensitive data. Implement encryption and tokenization and use key management practices to securely manage encryption keys.
- Monitor and audit cloud usage continuously. Use CASB logging and reporting to generate audit trails and compliance reports. Use the security dashboard to help detect and record anomalous activities, unauthorized access attempts, and compliance violations.
- Provide user training. Educate users about security risks associated with cloud usage and encourage them to report suspicious activities and adhere to best practices.
- Regularly update and patch CASB. Update the CASB service with the latest security fixes and regularly review security configurations and policies.
- Test and validate CASB configuration. Conduct regular penetration testing, vulnerability assessments, and CASB certificate checks to enforce security policies effectively, identify and remediate security gaps, and confirm the CASB platform is operating as intended.
- Follow cloud security trends. Proactively adapt the CASB strategy to address evolving security challenges.
How Does AppOmni Help Secure Cloud Environments?
AppOmni delivers an effective solution to the challenges of securing SaaS—a product that builds on the strengths of existing solutions like CASBs and incorporates features of other point solutions, such as compliance and data security software.
The AppOmni SaaS Security Posture Management solution deploys automation to continuously monitor applications for drift from established security baselines; discover security threats; protect SaaS environments from unnecessary risks; and ensure organizations adhere to compliance standards. The AppOmni approach lets organizations move rapidly and confidently to promote growth while ensuring security guardrails safeguard sensitive, business-critical data.
Learn more about AppOmni’s SSPM solutions.