How AppOmni secures Microsoft 365 and M365 Copilot
AppOmni combines deep SaaS and AI security posture management expertise with Microsoft 365 and M365 Copilot administrative knowledge to stay ahead of cyber attacks. We help IT security architects and vulnerability management teams manage security posture, implement configuration best practices, and monitor threats to your SaaS and AI integrations.
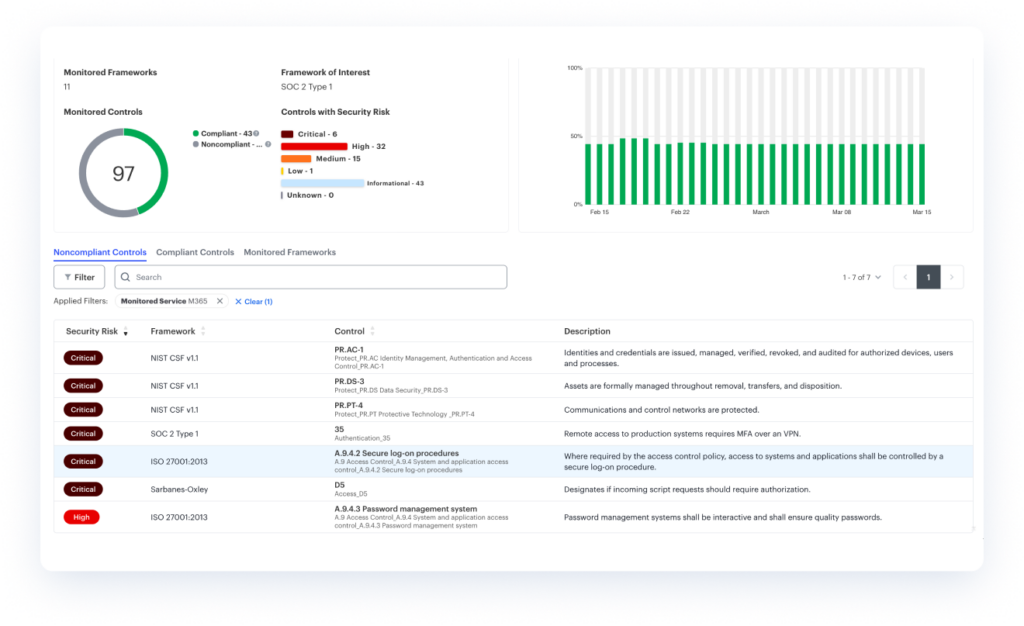
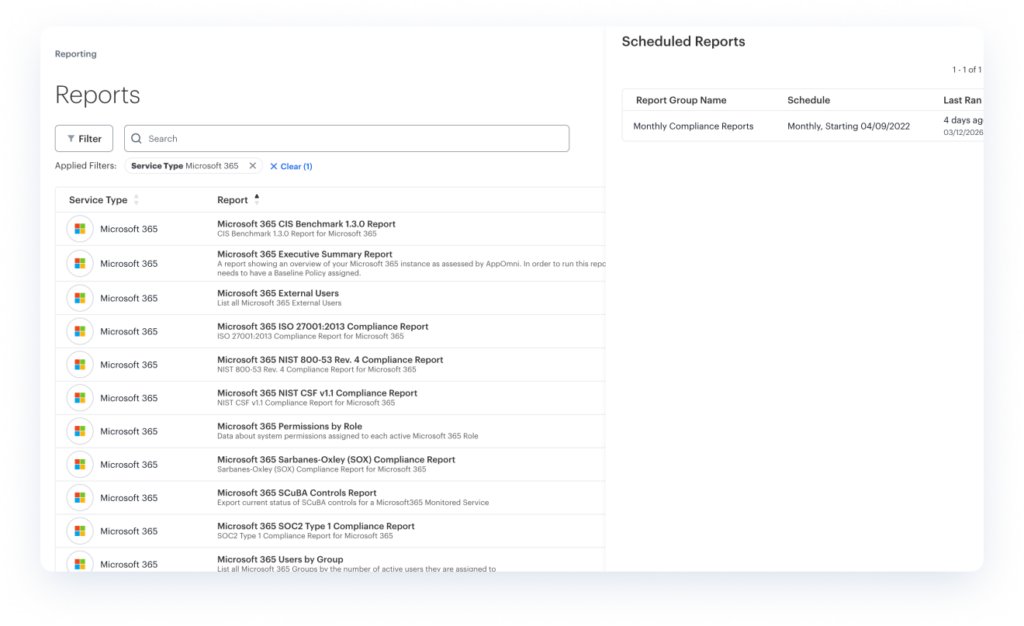
AppOmni maps to compliance and security policies for your enterprise
Use out-of-the-box baseline security policies and map to compliance frameworks for Teams, Exchange Online, SharePoint etc. This includes NIST CSF, GDPR, SOC2, HIPAA, and SCuBA compliance for federal civilian agencies.
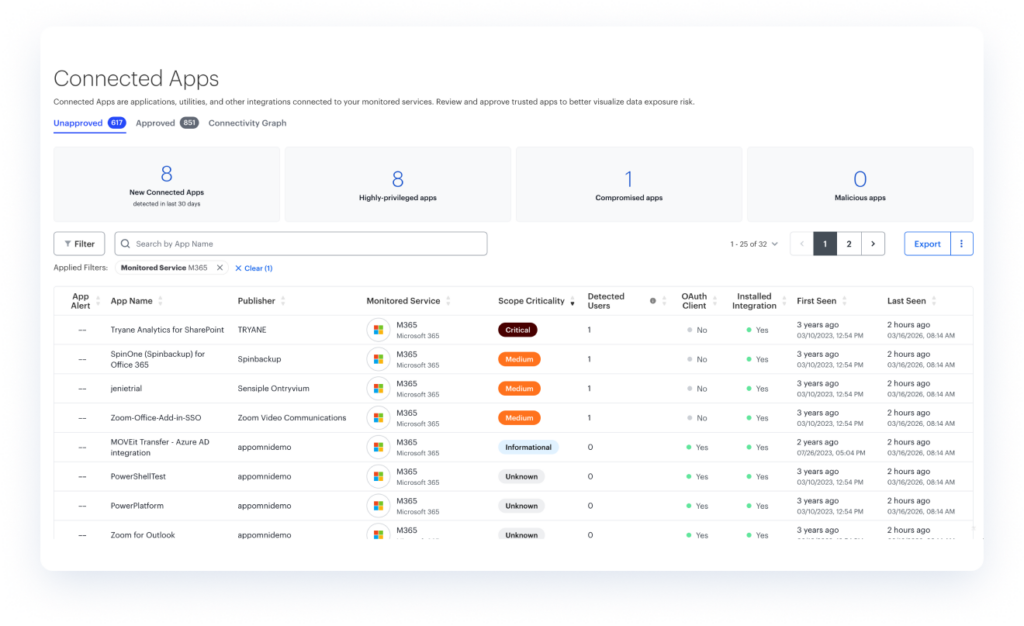
Discover and identify all SaaS and AI applications with third-party integrations
Oversee which SaaS and AI applications reside within your environment to manage known applications and uncover unknown applications and integrations to secure your posture. Plus, restrict OAuth scopes to minimize exposure, particularly in Teams, OneDrive, SharePoint, and Entra ID.
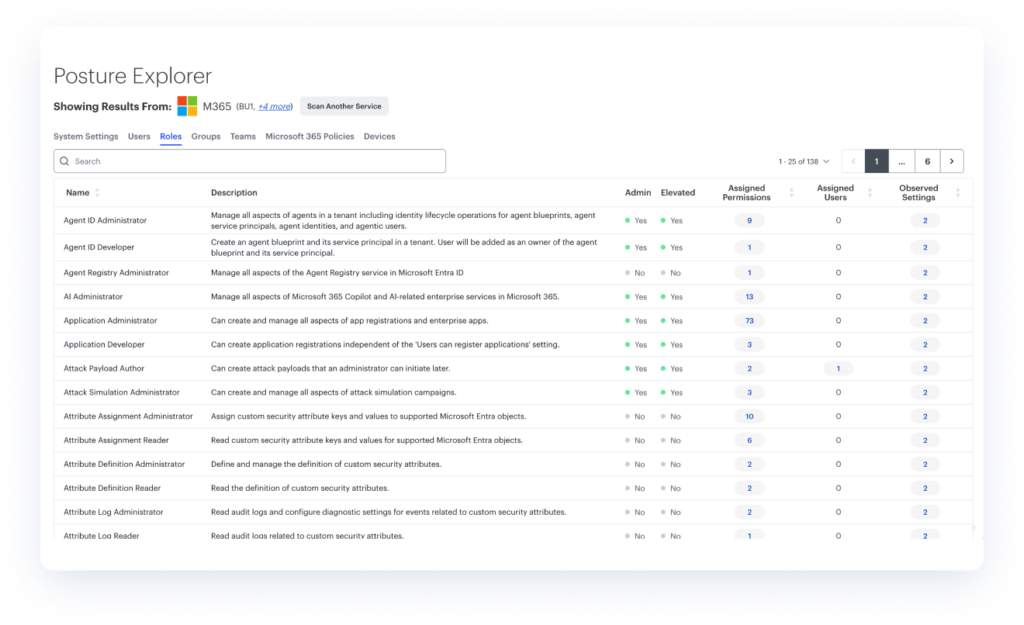
Implement Zero Trust and least-privilege best practices to strengthen your security posture
Govern role-based access controls (RBAC) for human and non-human identities (NHI) to ensure the ability to communicate with the correct data sources. Plus, surface and correct excessive agent permissions to tighten security posture.
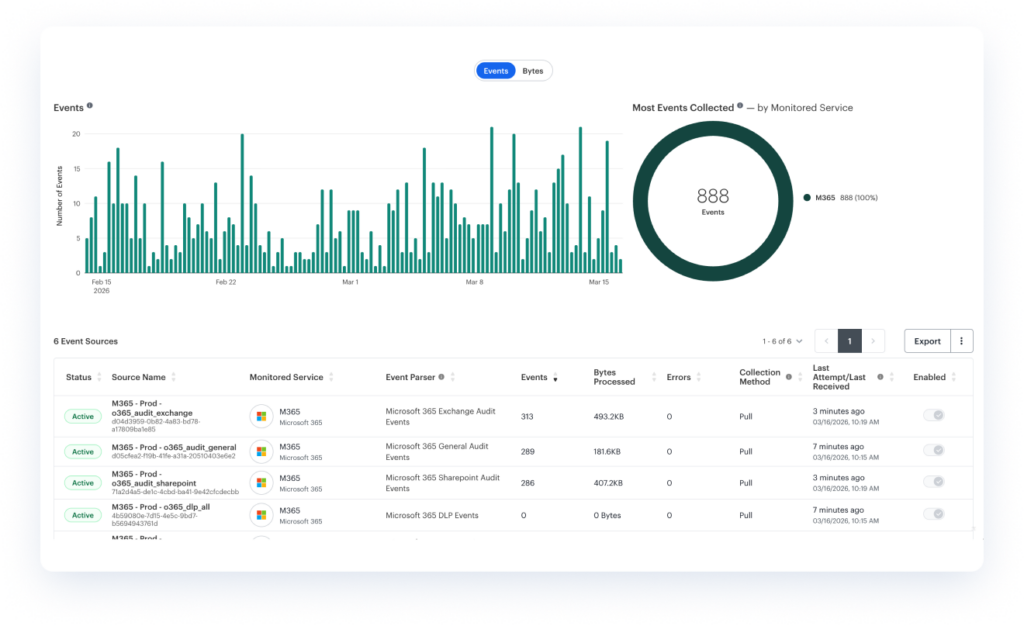
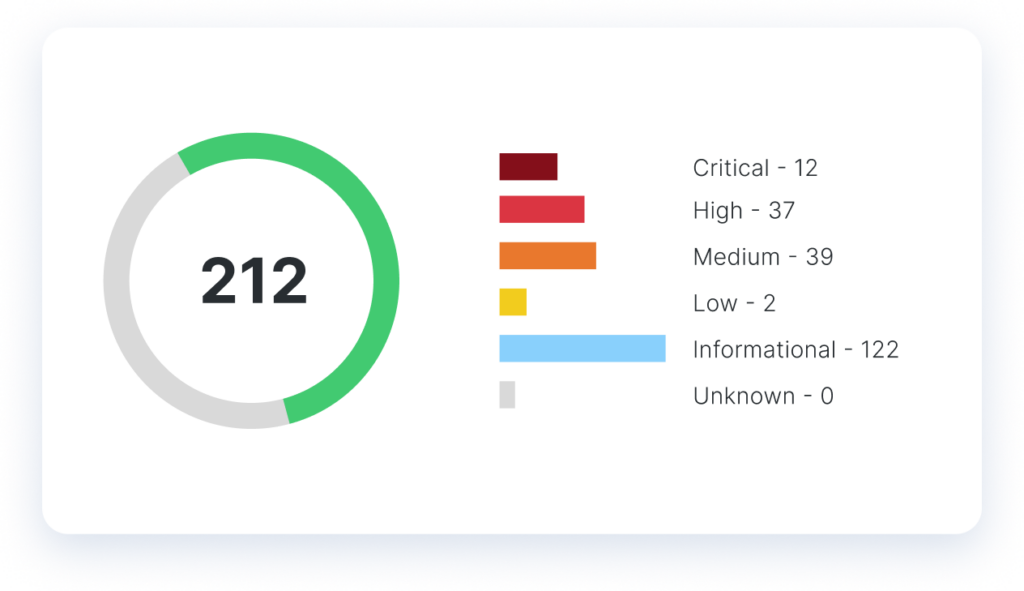
Observe and detect security and compliance risks and threats in real time
Continuously monitor, detect, and track risks and threats to your SaaS and AI applications and your security posture to maintain governance.
“Our administrator was able to on-board the M365 application over lunch.”
— Information Security and Risk Manager, Spencer Fane
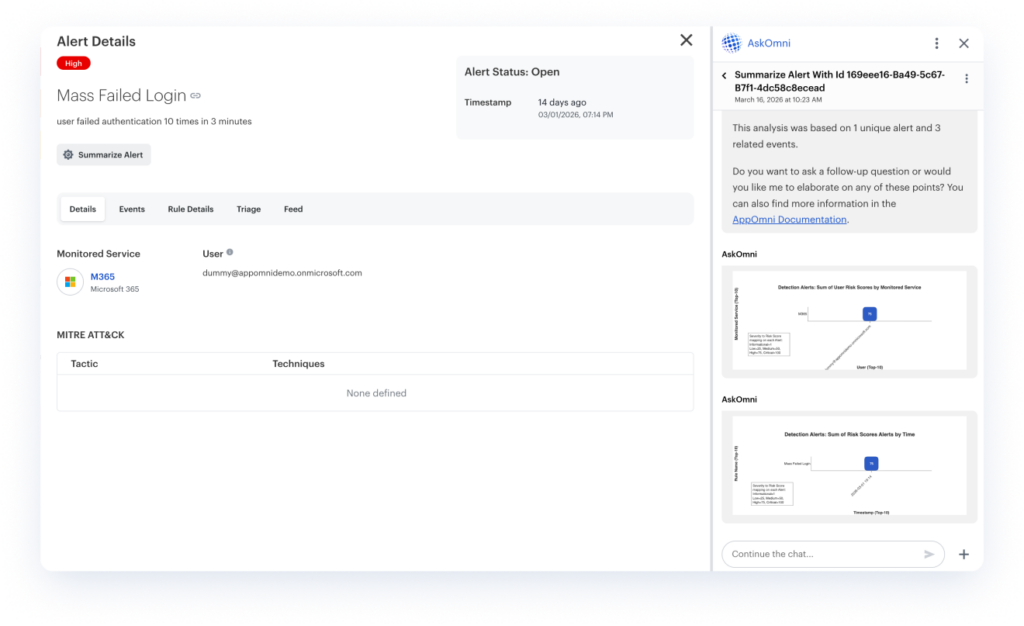
Alert, triage, and act to remediate any SaaS and AI threats
Enable alerts to execute workflows to triage communication to investigate and remediate configuration changes or threats detected within your environment.
Continuous threat and vulnerability research on M365
Microsoft 365 security monitoring through AppOmni Labs conducts continuous offensive threat research against Microsoft 365 to uncover new vulnerabilities and misconfiguration possibilities.

How AppOmni helps with Microsoft 365 and M365 Copilot security
- Agentless architecture that delivers continuous SaaS security monitoring.
- Strengthen account protection by closing gaps in MFA enforcement.
- Create and enforce “block” or “allow” policies for SharePoint groups to ensure only authorized users access sensitive data.
- Sync identities with Microsoft Entra ID for centralized access control across Microsoft 365 services.
- Validate Microsoft 365 settings against internal controls and frameworks like SOX, ISO 27001, and NIST.
- High-fidelity threat detection that integrates with existing SIEM / SOAR tools.
See what you’re missing
Attackers target Microsoft 365 and M365 Copilot because its broad use makes it a perfect target for account takeovers, data theft, and insider threats.
Get a free Microsoft 365 security assessment from AppOmni. Our team of experts will review your environment, provide vulnerability insight, and suggest remediations for your security team to strengthen your SaaS and agentic AI security and protect from M365 security vulnerabilities.
Latest Resources
-

EvilToken and Microsoft 365: A Familiar Attack Playbook, Scaled with AI
High-value M365 user orgs targeted by an AI-powered device code phishing campaign. Here’s how the EvilToken attack happened, and what prevention controls to take.
-
Trivy Scanner Compromise Explained and What it Means For Your SaaS and CI/CD Security
The Trivy supply chain compromise gave attackers a way to deliver malicious infostealer code. Learn how it happened and required remediation steps to audit your environment.
-

What is the Salesforce GraphQL Exploit and What You Should Do
Salesforce GraphQL exploit exposed misconfigured guest data in Experience Cloud. Learn how it happened and how to prevent exposure.