Compliance for SaaS
Make SaaS compliance easy. Simplify, secure, and sustain standards.
CHALLENGE
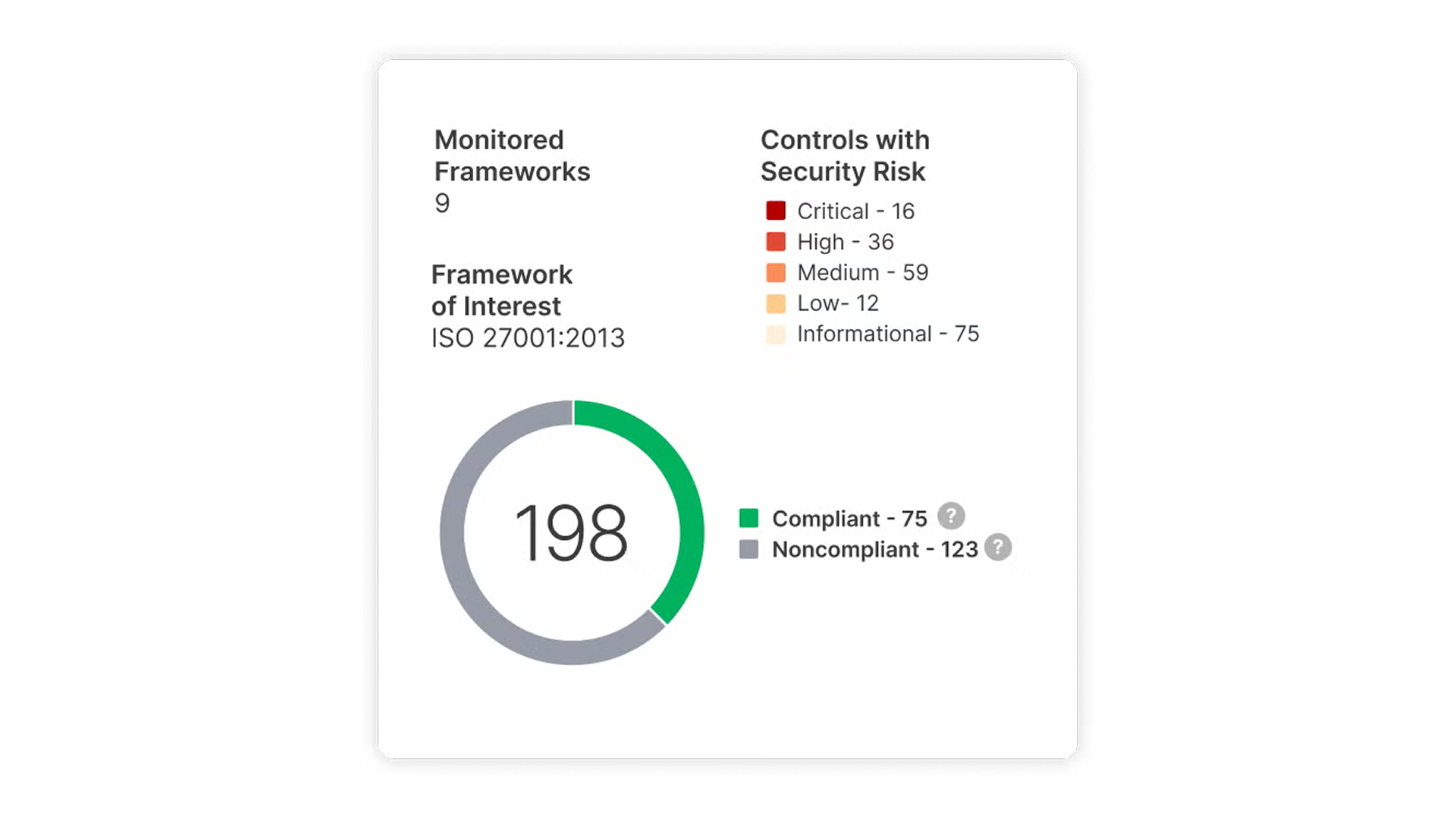
SaaS applications rely on external integrations, access policies, and configurations which if set up incorrectly, can violate security and privacy laws. From HIPAA, Sarbanes-Oxley to SOC II, AppOmni ensures your SaaS applications align and comply with regulatory SaaS compliance standards.
How AppOmni Compliance Secures SaaS
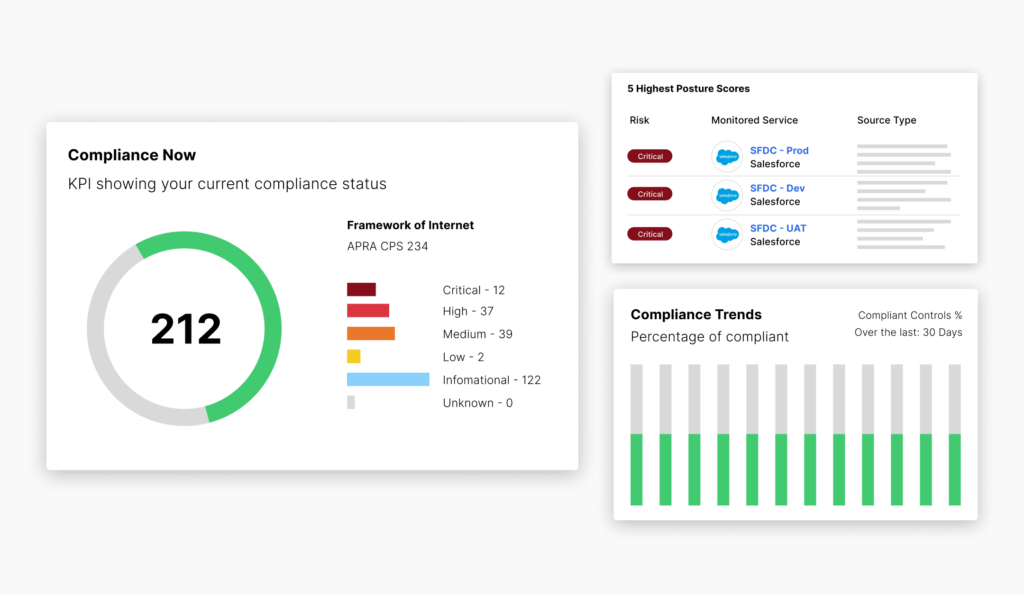
AppOmni enforces SaaS security controls, monitors for policy drift, and delivers audit-ready evidence to support compliance with standards like ISO, SOC 2, and HIPAA.
Detect SaaS Shadow IT
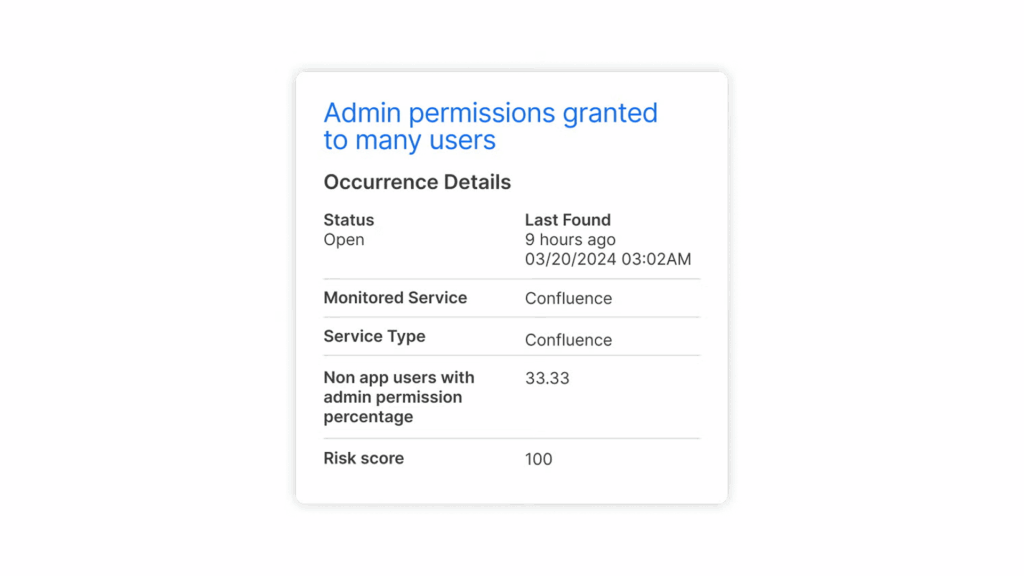
Detect unauthorized applications connected to your managed SaaS applications and gain insights into risks and incorrect user permissions.
Automation
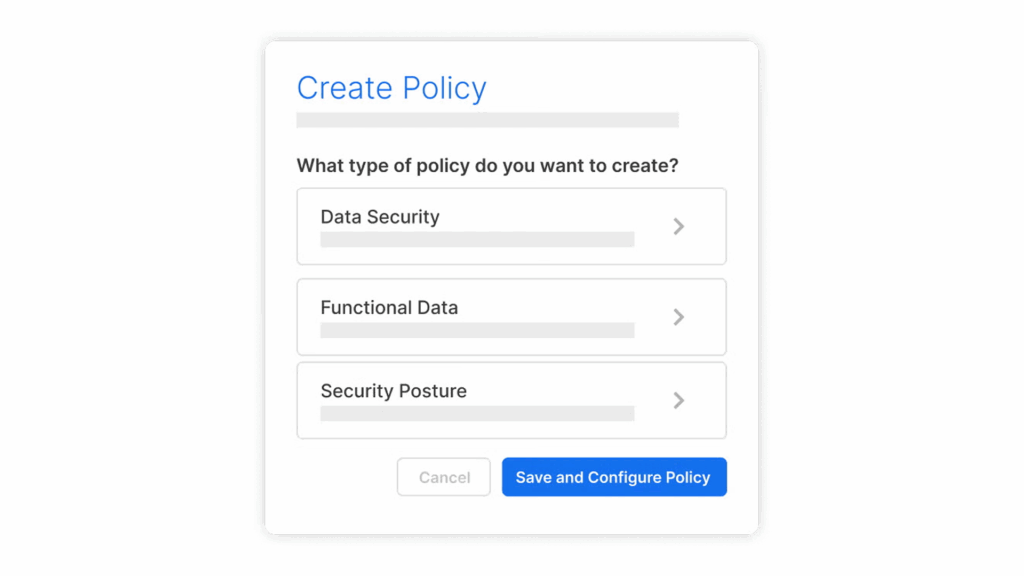
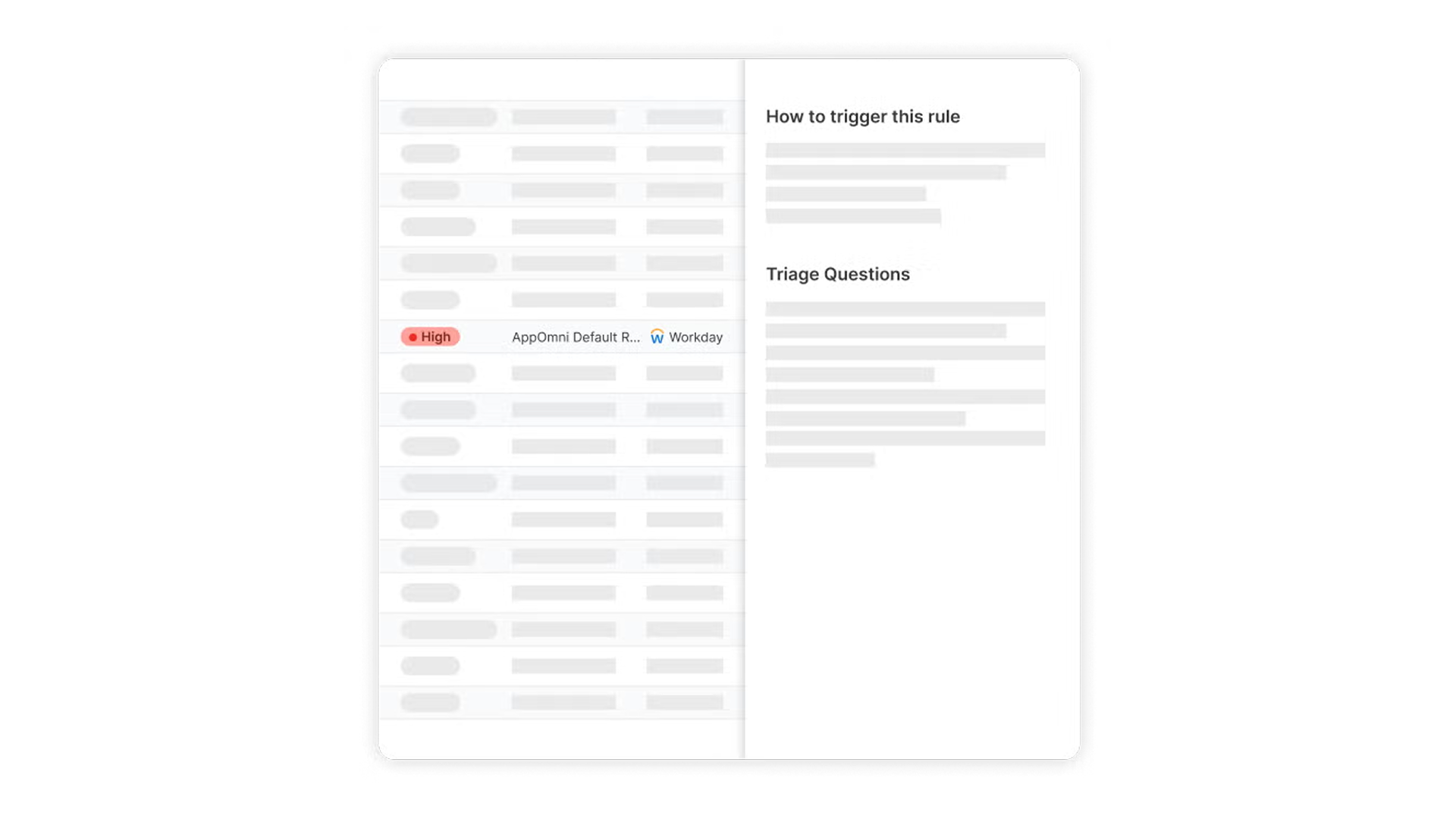
Reduce tedious app by app validation of SaaS compliance checks. Use real-time insights and alerts to prevent potential violations and enhance overall SaaS security posture.
Identify, Prioritize & Remediate Misconfigurations
Utilize policy baselines or custom frameworks to alert on non-compliance. Ensure compliance using guided remediation steps.
Key Features
Supporting Federal SaaS Security and Resilience
AppOmni has been granted Federal Risk and Authorization Management Program (FedRAMP) Moderate Authority to Operate (ATO). Agencies can confidently adopt AppOmni’s SaaS Security Platform to secure their SaaS ecosystem, meet critical compliance requirements, and optimize data protection across multiple platforms.

Related Content
-
How to add AI to an existing product (without annoying users)
“It may cost much more time and money to solve the same problem with AI than by a statistics and data science approach.” — Melissa Ruzzi, Sr. Director of AI, AppOmni.
-

CSPM vs SSE/SASE vs CASB vs SSPM: Who Secures What
Learn how CSPM, SASE, CASB, and SSPM differ, and where each fits in securing cloud infrastructure, access, and SaaS applications. Discover the critical visibility gaps in modern security stacks.
-

The Top 3 Ways Criminals Use AI in Cyber Attacks
AI-driven SaaS security risks grow fast. Here’s what to watch out for and how to prevent breaches.
“I needed to get a better understanding of the overall attack surface, our portfolio of applications, and their configurations and data exposure risks.”
Wai Sheng Cheng
Information Security and Risk Manager, Spencer Fane

Cut compliance reporting time by 90%. What took days now takes minutes.
Centralize controls, map requirements, and prove compliance fast.