Component Library
Alerts – Site Header Templates (“Edit Site”)
CTA – Stacked
How’s your ServiceNow posture?
Join our experts as they walk through a practical framework to assess and improve the security posture of your ServiceNow tenant. Learn how to address common pitfalls that lead to data exposure or audit gaps.
Count Up
131M+
SaaS users protected
260M+
Exposed data records secured
78B+
Events analyzed monthly
2M+
Third-party app installations found
Key Takeaways for long-form blogs
Infobox – Key Takeaways
- Add copy here, keep short and concise using bulletpoints.
- Bulletpoint 2
- Bulletpoint 3
Infobox bulleted headline – Key Takeaways
Add copy here, keep short and concise in paragraph form.
Table
| Header Label | Header Label | Header Label | Header Label | Header Label |
|---|---|---|---|---|
| Testing | Testing | Testing | Testing | Testing |
| Testing | Testing | Testing | Testing | Testing |
| Testing | Testing | Testing | Testing | Testing |
Accordion Block & Default Setup
Image Gallery




Pull Quote
“This is an example of a pull quote within a body of text like in a post. Lorem ipsum dolor sit amet, consectetur adipiscing elit. Etiam eu turpis molestie, dictum est worem ipsum.”
Jane Doe
Company Name
Image Variations

Maecenas vitae tincidunt eros, vel tincidunt nibh. Nulla dictum lacus sed neque auctor, non finibus nulla iaculis. Fusce varius varius tortor a rutrum. Nam sodales a lectus et vehicula. Nam non nunc risus. Curabitur scelerisque est eget mi consectetur egestas.

Norem ipsum dolor sit amet, consectetur adipiscing elit. Etiam eu turpis molestie, dictum est a, mattis tellus. Sed dignissim, metus nec fringilla accumsan, risus sem sollicitudin lacus, ut varius volutpat turpis sed lacinia. Nam eget mi in purus lobortis eleifend. Sed nec ante dictum sem condimentum
Pellentesque malesuada mollis purus nec lobortis. Praesent dignissim nunc non tellus posuere, in blandit mauris viverra. Etiam et vulputate quam. Suspendisse posuere velit sit amet urna fermentum, at vestibulum

Norem ipsum dolor sit amet, consectetur adipiscing elit. Etiam eu turpis molestie, dictum est a, mattis tellus. Sed dignissim,
Block Pattern – Featured Text
Enterprise-Level SaaS Security
SaaS security is complex. And without a standard security settings framework, IT and Security teams find it nearly impossible to protect the dozens — if not hundreds — of SaaS apps they support.
Block Pattern – Media & Text Block – Standard Left

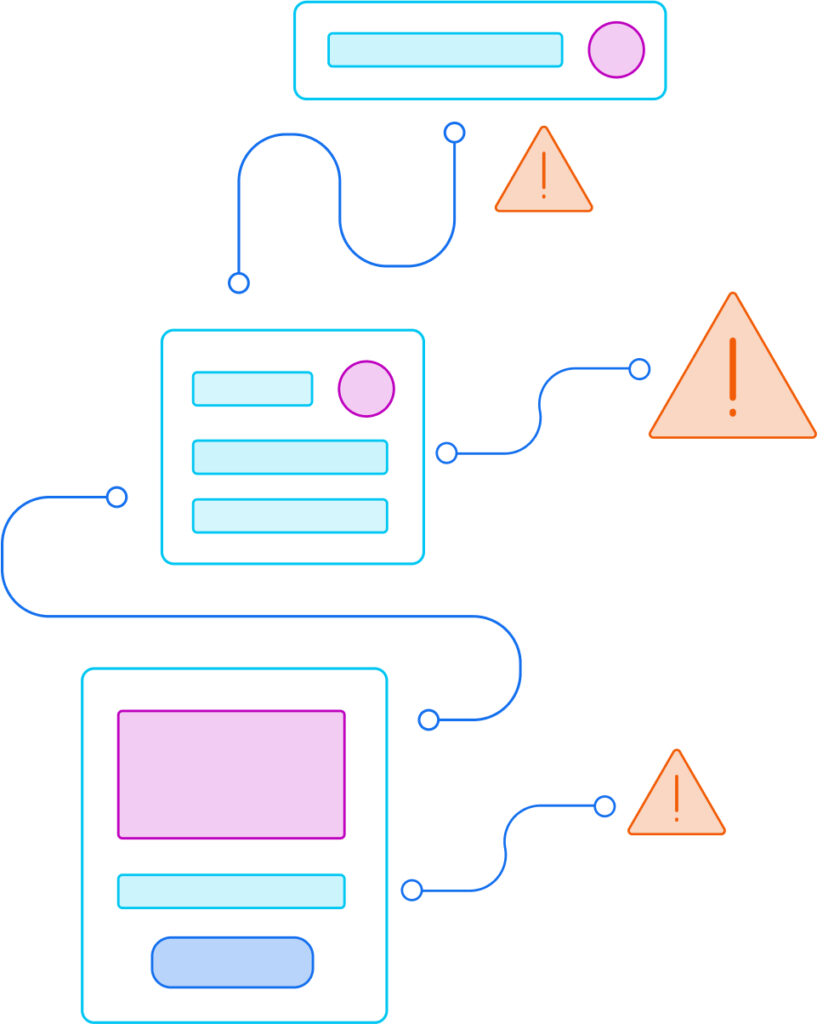
Securing Current SaaS Apps
Companies need to continuously understand their compliance levels and identify common SaaS data threats such as suspicious logins, brute force attempts, OAuth issues, over-privileged user access, and configuration drift.
How AppOmni Can Help:
- Identify application misconfigurations & policy violations
- Alert on suspicious activity
- Continuously monitor compliance
Customer Use Case: AppOmni helped a large national bank secure Salesforce data after moving data from an on-prem solution to the cloud.
Block Pattern – Media and Text Block – Standard Right
Initial SaaS Implementation
When deploying new SaaS applications, teams are tasked with leveraging a minimum security baseline to ensure SaaS apps are configured properly from initial deployment.
How AppOmni Can Help:
- Identify application misconfigurations & policy violations
- Alert on suspicious activity
- Continuously monitor compliance
Customer Use Case: AppOmni helped a large national bank secure Salesforce data after moving data from an on-prem solution to the cloud.
Block Pattern – Cover – Large

Unmatched Security for Your SaaS Apps
AppOmni SaaS security makes it easy for security and IT teams to protect and monitor their entire SaaS environment.
Block Pattern – Cover – Small

Resource Hub
A collection of our latest articles, videos, news, and more.
Block Pattern – Cover – Page Title
Enterprise-Level SaaS Security
Logo Carousel
Tabs
Taxonomy Filters
Query Loop Patterns:
-

The Top 3 Ways Criminals Use AI in Cyber Attacks
AI-driven SaaS security risks grow fast. Here’s what to watch out for and how to prevent breaches.
-

Synthetic identities are the next step for security in an agentic age
The trick is finding the balance between allowing staff to utilize AI and ensuring they deploy it responsibly.
-

Vercel Confirms Cyber Incident After Sophisticated Attacker Exploits Third‑Party Tool
Cory Michal, CISO at AppOmni, traced the breach back to the OAuth access Context.ai provided to the Vercel employee’s Google Workspace account.
Featured Resources
SaaS security is complex. And without a standard security settings framework, IT and Security teams find it nearly impossible to protect the dozens — if not hundreds — of SaaS apps they support.
-

The Top 3 Ways Criminals Use AI in Cyber Attacks
AI-driven SaaS security risks grow fast. Here’s what to watch out for and how to prevent breaches.
-
Synthetic identities are the next step for security in an agentic age
The trick is finding the balance between allowing staff to utilize AI and ensuring they deploy it responsibly.
-
Vercel Confirms Cyber Incident After Sophisticated Attacker Exploits Third‑Party Tool
Cory Michal, CISO at AppOmni, traced the breach back to the OAuth access Context.ai provided to the Vercel employee’s Google Workspace account.
-
Beyond the hype: The critical role of security in responsible AI development
Melissa Ruzzi shares why AI pipelines need zero trust principles and continuous human oversight.
-
The Top 3 Ways Criminals Use AI in Cyber Attacks
AI-driven SaaS security risks grow fast. Here’s what to watch out for and how to prevent breaches.
-
Synthetic identities are the next step for security in an agentic age
The trick is finding the balance between allowing staff to utilize AI and ensuring they deploy it responsibly.
-
Vercel Confirms Cyber Incident After Sophisticated Attacker Exploits Third‑Party Tool
Cory Michal, CISO at AppOmni, traced the breach back to the OAuth access Context.ai provided to the Vercel employee’s Google Workspace account.
-
Beyond the hype: The critical role of security in responsible AI development
Melissa Ruzzi shares why AI pipelines need zero trust principles and continuous human oversight.
-
When AI Agents Serve Shared Workspaces, Authorization Must Follow the Audience
Aaron Costello at AppOmni found that Virtual Agent and Now Assist trusted a hardcoded secret plus email address for account linking.
-
Supply-chain attack against open source projects could have big impact
Cory Michal, VP of Security and IT at AppOmni, weighs in on the large-scale impact of the Trivy compromise.
-
Can Anthropic Keep Its Exploit-Writing AI Out of the Wrong Hands?
“No one can ever keep anything 100% out of attackers’ hands.” — Melissa Ruzzi, Director of AI at AppOmni.
-
EvilToken and Microsoft 365: A Familiar Attack Playbook, Scaled with AI
High-value M365 user orgs targeted by an AI-powered device code phishing campaign. Here’s how the EvilToken attack happened, and what prevention controls…
-
Building Trust Into Automated Cybersecurity Decisions
Melissa Ruzzi shares in Cyber Security Tribe how organizations build trust in agentic AI cybersecurity decisions with governance, explainability, and accountability.
-
Top 10 Best SaaS Security Posture Management (SSPM) Tools 2026
AppOmni is selected for its enterprise-grade capabilities, focusing on deep configuration management & policy enforcement across critical SaaS apps.
- BOLD not bold
- not bold BOLD
- list item
-

The Top 3 Ways Criminals Use AI in Cyber Attacks
AI-driven SaaS security risks grow fast. Here’s what to watch out for and how to prevent breaches.
/
-

Synthetic identities are the next step for security in an agentic age
The trick is finding the balance between allowing staff to utilize AI and ensuring they deploy it responsibly.
-
Vercel Confirms Cyber Incident After Sophisticated Attacker Exploits Third‑Party Tool
Cory Michal, CISO at AppOmni, traced the breach back to the OAuth access Context.ai provided to the Vercel employee’s Google Workspace account.
-
Beyond the hype: The critical role of security in responsible AI development
Melissa Ruzzi shares why AI pipelines need zero trust principles and continuous human oversight.
-
When AI Agents Serve Shared Workspaces, Authorization Must Follow the Audience
Aaron Costello at AppOmni found that Virtual Agent and Now Assist trusted a hardcoded secret plus email address for account linking.
OUR VALUE TO THE MODERN ENTERPRISE
Deep Posture Inspection. Real-Time Risk Identification at Scale.
With AppOmni, global customers across industries can secure their SaaS ecosystems at scale. Hear how they established visibility on potential exposed data, prioritized granular SaaS application control, and achieved compliance through one platform.