AI Security Posture Management Definition
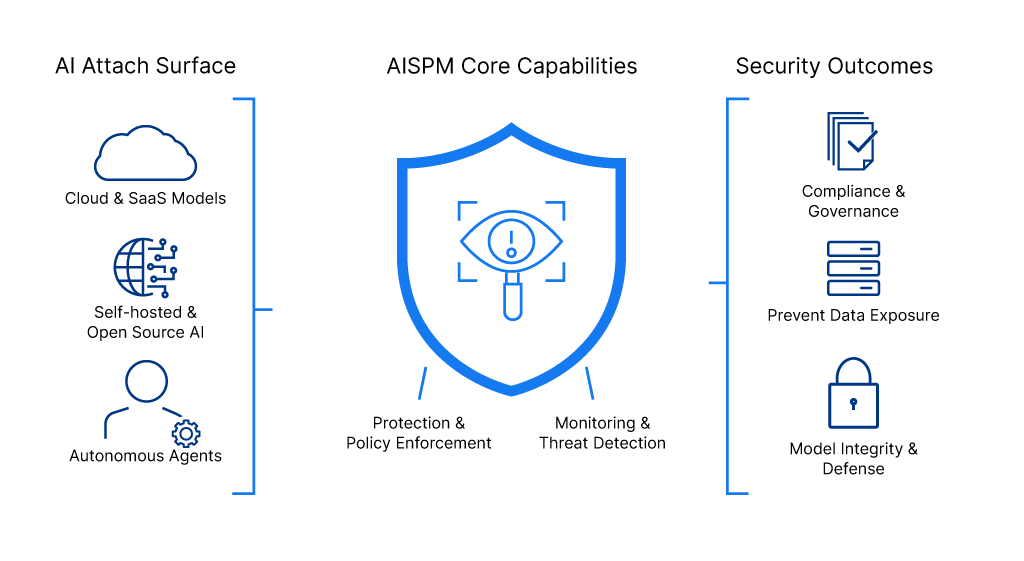
AI Security Posture Management (AISPM) is a cybersecurity discipline that secures artificial intelligence systems by discovering, monitoring, and protecting AI models, services, agents, and their associated data across enterprise environments.
AISPM FAQs
What is AI Security Posture Management?
AI Security Posture Management represents a critical evolution in enterprise cybersecurity as organizations rapidly integrate artificial intelligence into their core business operations. AISPM solutions provide visibility into AI deployments, detect misconfigurations and vulnerabilities, enforce access controls and compliance policies, and identify anomalous behavior or security threats specific to AI infrastructure across the AI lifecycle from development to production. As AI adoption accelerates, the unique security challenges introduced by AI models, training data, and autonomous agents demand specialized protection that traditional cloud security platforms cannot adequately address.
The proliferation of AI technologies has created an expansive attack surface that extends beyond conventional IT infrastructure. Organizations deploy AI across multiple environments including cloud-hosted models, self-hosted open-source frameworks, software development kits embedded in applications, and increasingly autonomous AI agents that operate with elevated privileges. These AI systems process vast amounts of sensitive data, make autonomous decisions, and interact with critical business systems, creating risks such as data exposure, model theft, prompt injection attacks, and AI-powered social engineering. Without proper AISPM controls, security teams lack visibility into shadow AI deployments, cannot detect when AI models contain sensitive information in training data, and struggle to identify when threat actors compromise AI services or manipulate model behavior.
How Does AISPM Differ from Other Security Posture Management Solutions?
AI Security Posture Management and SaaS Security Posture Management (SSPM) serve complementary but distinct roles within enterprise cybersecurity strategies, with AISPM addressing the unique security challenges introduced by artificial intelligence systems that SSPM was not designed to handle. SSPM focuses on securing SaaS applications by monitoring configurations, user permissions, data sharing settings, third-party integrations, and compliance posture across platforms like Salesforce, Microsoft 365, Google Workspace, and ServiceNow. While SSPM excels at identifying misconfigurations in SaaS applications and managing access controls for human users, it lacks the specialized capabilities required to secure AI models, training data pipelines, autonomous agents, and the complex AI infrastructure that increasingly powers modern SaaS environments.
AISPM addresses security gaps that existing tools like Cloud Security Posture Management (CSPM), Data Security Posture Management (DSPM), and Application Security Posture Management (ASPM) were not designed to handle. While CSPM secures cloud infrastructure and DSPM protects data repositories, AISPM specifically tackles AI-specific risks including model poisoning, training data contamination, exposed API keys to AI services, misconfigured AI endpoints with public access, and autonomous agent behavior that deviates from intended operations. By extending security posture management principles into the AI domain, AISPM enables organizations to safely harness AI’s transformative potential while maintaining comprehensive security controls, regulatory compliance, and protection against both external threat actors and insider risks that target AI infrastructure as a high-value attack vector.
The relationship between SSPM and AISPM becomes increasingly important as SaaS platforms embed AI capabilities directly into their offerings. For example, Salesforce’s Einstein AI, Microsoft’s Copilot, ServiceNow’s AI agents, and other embedded AI features create scenarios where both SSPM and AISPM are essential. SSPM monitors the SaaS application’s security posture and user access controls, while AISPM specifically secures the AI models, monitors autonomous agent behavior, protects training data from exposure, and detects AI-specific attacks like prompt injection or model manipulation. Organizations deploying AI-powered SaaS applications need both disciplines working in concert: SSPM ensures the SaaS platform itself remains secure and properly configured, while AISPM provides the specialized protection required for the AI systems operating within and across those platforms, creating a comprehensive security framework that addresses both traditional SaaS risks and emerging AI-specific threats.
AI Security Risks Addressed by AISPM
Organizations implementing AISPM programs protect against a comprehensive range of AI-specific security threats and vulnerabilities that can compromise artificial intelligence systems and the sensitive data they process. AISPM solutions provide proactive defense across the entire AI attack surface, from model development through production deployment.
Key AI Security Risks AISPM Prevents:
- Shadow AI and unauthorized deployments – Unmanaged AI models, services, and tools deployed without security oversight create visibility gaps where threat actors can exploit unmonitored systems and sensitive data exposure occurs without detection.
- Model poisoning and training data manipulation – Attackers inject malicious data into training datasets or corrupt model weights to alter AI behavior, cause incorrect outputs, embed backdoors, or create models that leak sensitive information when prompted.
- Data exposure and leakage – AI models accidentally trained on sensitive data including PII, PHI, financial records, or proprietary information can inadvertently expose this data through model outputs, API responses, or when threat actors extract training data through inference attacks.
- Misconfigured AI services and public exposure – Improperly configured AI endpoints, publicly accessible model APIs, unencrypted data stores, and overly permissive network settings allow unauthorized access to AI infrastructure and enable model theft or data exfiltration.
- Compromised API keys and authentication tokens – Exposed credentials for AI services like OpenAI, Hugging Face, Azure OpenAI, and other platforms grant attackers the ability to make unauthorized API calls, access models, manipulate outputs, or generate massive usage costs.
- Prompt injection and jailbreaking attacks – Malicious prompts manipulate AI models to bypass safety controls, execute unintended actions, access restricted information, or behave in ways that violate security policies and expose sensitive data.
- Autonomous agent threats and privilege escalation – AI agents operating with elevated permissions can be compromised to move laterally across systems, escalate privileges beyond intended scope, access unauthorized resources, or execute malicious commands autonomously.
- AI-powered social engineering and deepfakes – Threat actors leverage generative AI to create convincing phishing attacks, deepfake videos or audio, fraudulent identities, and sophisticated social engineering campaigns that traditional security controls struggle to detect.
- Insider threats and accidental misuse – Well-intentioned users accidentally exposing sensitive data to AI tools, employees using unauthorized AI services for business tasks, or malicious insiders exploiting AI access to exfiltrate confidential information or sabotage models.
- Compliance violations and regulatory risks – AI systems processing regulated data without proper controls, lack of audit trails for AI decisions, inability to demonstrate AI governance, and failure to meet industry-specific requirements for AI usage create legal liability and financial penalties.
Benefits of AI Security Posture Management
Organizations that implement comprehensive AISPM programs gain the visibility and control necessary to safely accelerate AI adoption while protecting against emerging threats that specifically target artificial intelligence infrastructure. Through data security posture management for AI, enterprises discover shadow AI deployments that security teams didn’t know existed, identify AI models and training data that contain sensitive information, detect misconfigured AI services with public exposure, and flag exposed API keys before attackers can exploit them. This proactive approach transforms AI security from reactive incident response into continuous risk management, enabling enterprises to confidently deploy AI technologies across critical business operations without introducing unacceptable security gaps or compliance violations.
Beyond threat prevention, AISPM provides operational advantages that extend across the entire organization. Security teams gain centralized visibility into all AI assets and their risk profiles, eliminating the manual effort required to track AI deployments across cloud environments, SaaS applications, and development pipelines. Automated monitoring and behavioral analytics reduce alert fatigue by surfacing only high-priority threats specific to AI systems, while integration with existing security infrastructure ensures seamless operation alongside CSPM, DSPM, and SSPM tools. Organizations implementing AISPM report faster incident response times for AI-related security events, improved compliance posture with AI governance frameworks, reduced costs from preventing AI-specific breaches, and the ability to safely scale AI initiatives without proportionally increasing security team headcount – ultimately enabling innovation while maintaining the robust security controls that modern enterprises require.
Considerations for AISPM Software and Tools
Selecting the right AISPM software requires careful evaluation of capabilities that address the full spectrum of AI security challenges facing modern enterprises. Organizations should prioritize AI security posture management tools that provide agentless discovery and continuous monitoring across all AI deployments – including managed services like Azure OpenAI and Amazon Bedrock, self-hosted models, open-source frameworks, and autonomous AI agents. The best AI security posture management software delivers comprehensive AI inventory management with automatic detection of shadow AI, behavioral analytics that identify anomalous model behavior and potential compromise, sensitive data classification within training datasets, misconfiguration detection for AI services and endpoints, and exposed credential scanning across code repositories. AISPM vendors should demonstrate proven integration capabilities with existing security infrastructure including CSPM, DSPM, SSPM, and SIEM platforms, ensuring unified visibility without creating additional tool sprawl or alert fatigue.
When evaluating AISPM tools, enterprises must consider several critical factors beyond core security features. Deployment complexity and developer friction significantly impact adoption as solutions requiring extensive agent installation or code changes often fail to achieve comprehensive coverage, making agentless approaches preferable for rapid deployment and complete visibility. Scalability becomes essential as AI usage expands; AISPM software must handle growing inventories of models, agents, and services without performance degradation. Compliance and governance capabilities should include pre-built frameworks for AI-specific regulations, automated audit trail generation, and policy enforcement that adapts to organizational requirements. Organizations should also evaluate vendor expertise in AI security, platform maturity with proven enterprise deployments, support for multi-cloud and hybrid environments, and the solution’s ability to evolve alongside rapidly advancing AI technologies, ensuring the AISPM investment delivers long-term value as artificial intelligence becomes increasingly central to business operations.
AI Security Posture Management for SaaS Applications
AppOmni brings AI security posture management capabilities to the SaaS layer, where most enterprise AI is actually deployed. As AI capabilities become default features in Salesforce, Microsoft 365, ServiceNow, Google Workspace, and other business-critical applications, traditional AISPM solutions lack the application-layer visibility needed to secure them. AppOmni fills that gap, combining SSPM and AISPM in a single platform.
The AppOmni platform discovers AI features and integrations across your SaaS environment, monitors how AI agents interact with sensitive data, detects misconfigurations in AI settings, and identifies new attack paths or data exposure risks before they become incidents, so security teams can embrace AI-powered productivity without sacrificing control.