Industry
SaaS Security for Tech Companies
In-depth visibility to prevent SaaS exposures and reduce attack surface.

How AppOmni Secures SaaS for Technology
Technology companies rely on a number of SaaS applications to serve their customers. With vast amounts of sensitive data and intellectual property, improper SaaS configurations can pose significant risks, with potential business disruptions. AppOmni reduces these risks by offering deep visibility and SaaS security insights, minimizing the attack surface, and safeguarding data for more comprehensive SaaS security in the tech sector.
Custom Alerting and Rulesets
Detect Configuration Deviations
UEBA & Security Analytics

Triage and Remediation Guidance
From Audit Fatigue to Automation: How Rightmove Conducted a SaaS Security Transformation
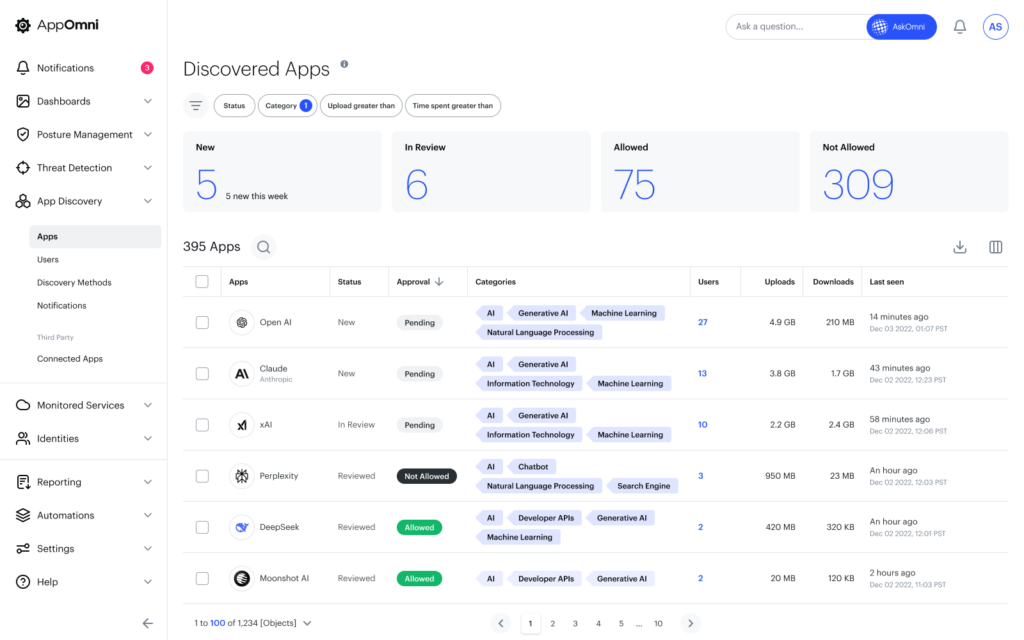
Monitoring SaaS apps at scale felt like playing whack-a-mole for Rightmove’s security team. As each department adopted its own tools—Slack, GitHub, NetSuite—security lost its grip on consistency. One standout moment: they discovered NetSuite was mistakenly counting customers as internal users, nearing a 100,000-user cap due to a misconfiguration no one had caught.
Enter AppOmni. The platform provided the clarity and automation Rightmove needed to regain control. By flagging misconfigured permissions, aligning app settings to policies, and enabling cross-team collaboration, AppOmni turned Rightmove’s fragmented SaaS sprawl into a streamlined security program. Now, instead of scrambling to audit, they preemptively secure every app.

5 Key Considerations and Checklist for Evaluating Your SaaS Security Solution
How Our SaaS and AI Security Platform Brings Value
AppOmni’s agentless architecture delivers continuous SaaS and AI security monitoring for your environment. Gain complete visibility and discover SaaS and AI connections. Receive real-time alerts, insights, and actionable remediation guidelines to prevent unauthorized access to your critical data and proactively block malicious activity. AppOmni provides a unified command center for all SaaS and AI applications across your enterprise.
Latest Resources
-

How SANS Institute Gained Visibility, Reduced Risk, and Streamlined Compliance
SANS Institute eliminated Salesforce visibility gaps, reduced critical risk by 40%, and doubled remediation capacity using AppOmni.
-
Bubble or no bubble, AI continues to define market
Melissa Ruzzi noted that AI has been promoted in ways that led to unrealistic, outsize assumptions about the technology’s power and capabilities.
-

AppOmni Wins Frost & Sullivan’s 2025 Technology Innovation Leadership Award
Frost & Sullivan named AppOmni the 2025 Technology Innovation Leader for its customer-first innovation, scalable SaaS protection, and leadership in the global SSPM market.