How to Secure Salesforce: Essential Best Practices to Protect SaaS Data
Learn how to secure Salesforce with best practices for identity management, OAuth governance, and continuous monitoring to prevent data breaches.
Resource Hub
Learn how to secure Salesforce with best practices for identity management, OAuth governance, and continuous monitoring to prevent data breaches.

High-value M365 user orgs targeted by an AI-powered device code phishing campaign. Here’s how the EvilToken attack happened, and what prevention controls to take.

“Repeated compromises of the same vendor in a short period suggest a persistent weakness,” said Cory Michal, CSO at AppOmni.
The Trivy supply chain compromise gave attackers a way to deliver malicious infostealer code. Learn how it happened and required remediation steps to audit your environment.

Salesforce GraphQL exploit exposed misconfigured guest data in Experience Cloud. Learn how it happened and how to prevent exposure.

This blog deeply analyzes the interplay between Virtual Agent API and Now Assist enabled in this exploit.
Aaron Costello uncovers how second-order prompt injection turns AI agents against their own systems. He explains how attackers exploit ServiceNow’s Now Assist and offers clear guidance on securing AI collaboration.

Turn SBOMs into supply chain defense with Heisenberg, an open source tool developed by Max Feldman and Yevhen Grinman. It stops risky pull requests (PRs) before they merge.

Spot UNC6040 vishing attacks, secure OAuth apps, boost SaaS security with AppOmni’s Threat Detection.
OAuth abuse exposes SaaS data. AppOmni’s threat detection and security posture management shut it down.
AppOmni’s latest research reveals 20+ OmniStudio security flaws, including 5 CVEs affecting Salesforce industry clouds. Learn how misconfigurations expose sensitive data and how to secure your org.
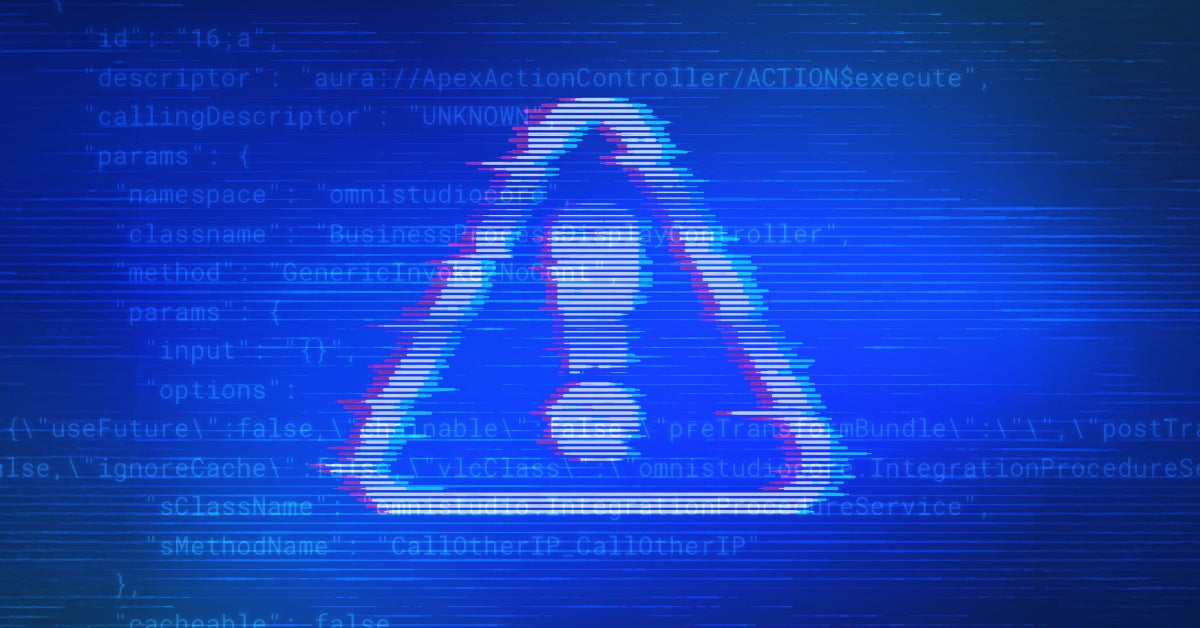
New research reveals critical security flaws in Salesforce industry clouds. Discover the risks and how to protect your organization now.

Discover what went wrong in the Commvault breach: How AppOmni’s powerful SaaS security platform steps in to stop threats before they strike.