ShinyHunters’ alleged breach of Woflow (a third-party SaaS provider) highlights a broader shift in SaaS attacks that started last summer with the Salesloft Drift breach. Rather than breaching individual organizations one by one, threat actors increasingly pursue upstream SaaS vendors with deep OAuth and API connections into multiple environments and then move laterally.
Whether confirmed or not, this incident is one of many that reveals SaaS-to-SaaS integrations, non-human identities, and OAuth tokens have expanded the attack surface beyond traditional controls. Securing SaaS today requires continuous monitoring to identify configuration drift, identity governance, and oversight of third-party connections, not just network-centric defenses offered by SSE and CASB solutions or the ad hoc audits so many organizations rely on.
Key takeaways
- Increasingly, attackers target integration-heavy SaaS vendors to gain downstream access at scale.
- OAuth tokens and non-human identities can function as critical vulnerability points if not tightly governed.
- Confidence in sanctioned SaaS apps often masks visibility gaps in configurations and third-party integrations, providing a false sense of security.
- Continuous SaaS security posture management and identity-centric monitoring is essential to reduce supply chain exposure.
The alleged ShinyHunters Woflow breach explained
ShinyHunters claims it breached Woflow, a third-party SaaS provider whose customers reportedly include Uber, DoorDash, and Walmart, and exfiltrated hundreds of millions of records. At the time of writing this (March 5, 2026), no public data sample has been released, and Woflow has not issued a public response.
Regardless of whether the claim is ultimately confirmed, this situation highlights a growing pattern in SaaS security. Threat actors are increasingly targeting integration-rich SaaS vendors to gain downstream access into multiple enterprise environments. We’ve seen this with the same pattern with the UNC6395 Salesloft/Drift breach, UNC6040’s Salesforce attack, and others more recently. This reflects a structural shift in how attackers approach SaaS data breaches.
ShinyHunters has developed a repeated, financially-motivated playbook built around exploiting trusted connections between third-party applications and major SaaS providers, and publicly naming victims through messaging platforms before releasing data samples. In several prior incidents, organizations later confirmed breaches after initial claims surfaced.
In extortion-driven campaigns, attackers often provide proof of compromise directly to victims before publishing any public sample. A delay in public disclosure does not necessarily mean anything for certain, but it may indicate negotiations are underway.
While we still need official confirmation about this specific claim in order to investigate further, we can still explore and unpack what this means about the evolving SaaS threat landscape.
SaaS supply chain attacks and extortion tactics have evolved
Within our complicated, interconnected SaaS ecosystems, business-critical data flows between CRM platforms, data processors, automation tools, analytics platforms, and AI-driven tools. Each integration relies on OAuth permissions, API tokens, and more to establish and maintain secure SaaS-to-SaaS connections.
So, when attackers compromise a vendor embedded in that ecosystem, they potentially gain indirect access into many organizations at once. This vulnerability creates an opportunity for attackers. Instead of breaching one enterprise, attackers target a shared SaaS provider and use its trusted integrations to move laterally or extract data.
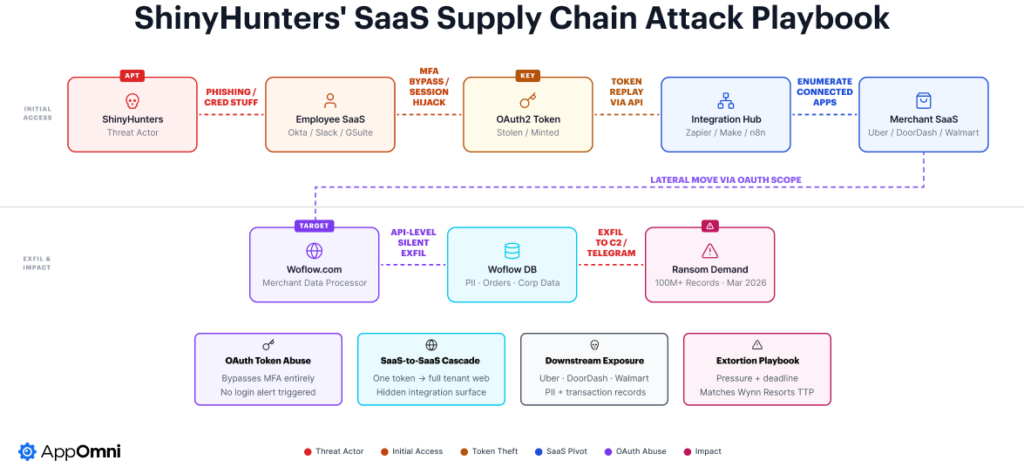
UNC6040 posted about the Woflow breach on its dark web blog and is threatening to leak the data on March 6, 2026, if the company refuses to comply with their demands. This mirrors the exact extortion cadence seen in the 2025 Salesforce CRM heist: claim the breach, set a deadline, release data in waves to turn up the heat.
This attack model aligns with the broader rise in SaaS-related security incidents. According to The State of SaaS Security Report, 75% of organizations experienced a SaaS-related security incident in the past year, yet 91% expressed confidence in their SaaS security posture largely due to the faith they place in these third-party SaaS tools (rather than maintaining security control themselves). That gap between confidence and outcome continues to widen as SaaS ecosystems grow more complex and oversight becomes more challenging.
SaaS-to-SaaS integrations expand the attack surface
SaaS environments are built on relationships between applications. OAuth tokens and API keys enable platforms to exchange data programmatically. These integrations often operate with elevated privileges to support automation and business workflows. This also means a significant (and growing) attack surface.
Key risk factors include:
- Over-permissioned OAuth scopes
- Long-lived access and refresh tokens
- Service accounts with broad data access
- Inherited permissions from highly privileged users
- Configuration drift over time
OAuth access tokens function as durable credentials. Because they are issued to trusted applications, activity can appear legitimate in audit logs (even when abused or behaving abnormally).
Traditional controls such as Multi-Factor Authentication (MFA) and Security Service Edge (SSE) solutions primarily secure human authentication flows and network access. They do not provide deep visibility into SaaS configurations, internal permission models, or third-party SaaS-to-SaaS connections.
Compromise increasingly occurs at the application layer, inside the SaaS control plane.
➡️ Download: OAuth Security Checklist
There is a visibility gap in SaaS security
Many organizations believe that sanctioned SaaS applications are secure because they passed an onboarding review or compliance audit. However, SaaS environments are dynamic. Permissions change. Integrations proliferate. Features are enabled or modified. New users and service accounts are introduced.
AppOmni’s research found that 89% of compromised organizations believed they had appropriate visibility into their SaaS environment at the time of the incident. Visibility without continuous validation and enforcement creates exposure.
Periodic audits are insufficient in environments where configurations can change daily. SaaS security requires continuous posture management, identity governance, and monitoring of SaaS-to-SaaS connections.
Integration-heavy vendors are high-value targets
A single compromise can create multiple downstream pressure points and turn into supply chain attacks. In extortion campaigns, that scale increases leverage; UNC6040 has claimed over 1.5 billion records across hundreds of companies.
Integration-rich vendors often:
- Aggregate sensitive operational data
- Maintain API access into multiple enterprise tenants
- Operate standardized integration models across customers
- Hold service accounts with elevated permissions
The attackers see it as far more efficient and financially-rewarding to target upstream SaaS providers with broad and extensive connectivity—via OAuth, APIs, tokens, or third-party SaaS connections—rather than attempting to breach individual enterprises one at a time.
How to strengthen SaaS supply chain security
Defending against these threats requires a strategy built for the security of SaaS and AI applications and the entire ecosystem they operate within.
Tackle OAuth token abuse and non-human identity risk
Modern SaaS environments rely heavily on non-human identities (NHI), including service accounts, API integrations, and AI agents. These identities frequently operate with broad permissions to enable automation and data exchange.
Security leaders should evaluate:
- Whether OAuth tokens are constrained by least privilege
- Whether token lifetimes are limited and rotated regularly
- Whether revocation mechanisms can be executed rapidly across applications
- Whether integration activity is monitored for anomalous behavior
- Whether third-party applications are continuously assessed for risk
AI-driven SaaS integrations add further complexity. AI agents often access large datasets to perform analytics, generate insights, or automate decisions. These agents should be governed under the same identity and access management principles applied to human users.
Without consistent oversight, non-human identities become persistent and under-monitored access pathways.
Reduce exposure across the SaaS and AI ecosystem
Securing SaaS supply chains starts with visibility and moves toward continuous monitoring and threat detection. Security leaders can take several steps to reduce risk here.
Discover your full SaaS attack surface
You can’t protect what you can’t see, so it’s critical to maintain a real-time inventory of sanctioned and unsanctioned applications connected to mission-critical SaaS platforms. Identify SaaS-to-SaaS connections, inherited permissions, and high-risk OAuth scopes, and restrict users’ ability to grant broad OAuth permissions without review.
Continuously govern app permissions
SaaS integrations should never be treated as “set and forget.” Organizations must enforce least-privilege access for OAuth-connected applications and service accounts, regularly review scopes and permission changes, and monitor for configuration drift that introduces unnecessary risk. Applying IP restrictions and contextual access controls where appropriate helps prevent bypass of security layers.
Extending Zero Trust principles into SaaS applications and SaaS-to-SaaS connections ensures that every access request is validated, regardless of whether it originates from a human or non-human identity. This approach shifts SaaS security from static audit cycles to a virtuous loop of continuous threat detection and posture management aligned with real-world risk.
Analyze behavior to detect threats
Configuration governance must be paired with behavioral monitoring to effectively reduce risk. Security teams should centralize and normalize SaaS activity logs to create consistent visibility across applications. By correlating identity context, configuration state, and user behavior, organizations can establish behavioral baselines for both human and non-human identities. This enables detection of abnormal token usage, suspicious data movement, unexpected geographic access patterns, or unusual privilege changes.
When posture insights and telemetry are combined, teams can identify toxic combinations (such as an over-permissioned OAuth app coupled with anomalous activity) before they escalate into data exposure. Correlating configurations, identities, behavior, and events is essential to prevent SaaS data breaches.
Transform SaaS security into an operational discipline
Taken together, these measures transform SaaS security from a periodic compliance exercise into a continuous, scalable operational program. Security leaders should focus on reducing the SaaS attack surface through proactive posture management, extending Zero Trust to third-party and AI-driven integrations, detecting threats with identity-centric context, and aligning business owners and security teams under clearly defined SaaS security ownership.
These measures help transform SaaS security from a periodic compliance exercise into an operational discipline.
Conclusion
Attackers have evolved. As business-critical data consolidates inside SaaS applications and flows between them through APIs and integrations, threat actors are increasingly targeting those trust relationships.
While still unconfirmed, the Woflow breach claim reflects a broader, repeatable pattern of compromising an integration-rich vendor, leveraging OAuth access and refreshing tokens as durable keys, and exploiting implicit SaaS-to-SaaS trust to enable quiet, API-level data access at scale. Since these tokens often bypass MFA and traditional login controls, the activity continues undetected.
At this point, security needs to extend deeper into the application layer. Continuous SaaS security posture management, strict governance of third-party OAuth, least-privilege enforcement for non-human identities, short token lifetimes, and rapid revocation capabilities are no longer optional controls. Organizations that operationalize this level of integration-aware, identity-centric SaaS security will reduce exposure and (hopefully) avoid the next supply chain-driven breach.
