The SaaS Due Diligence Questionnaire (DDQ), powered by AppOmni’s Event Maturity Matrix (EMM), helps security teams identify and close these gaps. Together, they provide a structured way to evaluate SaaS audit logs, assess SIEM integration, and ensure security-critical events are captured, accessible, and actionable across your environment.
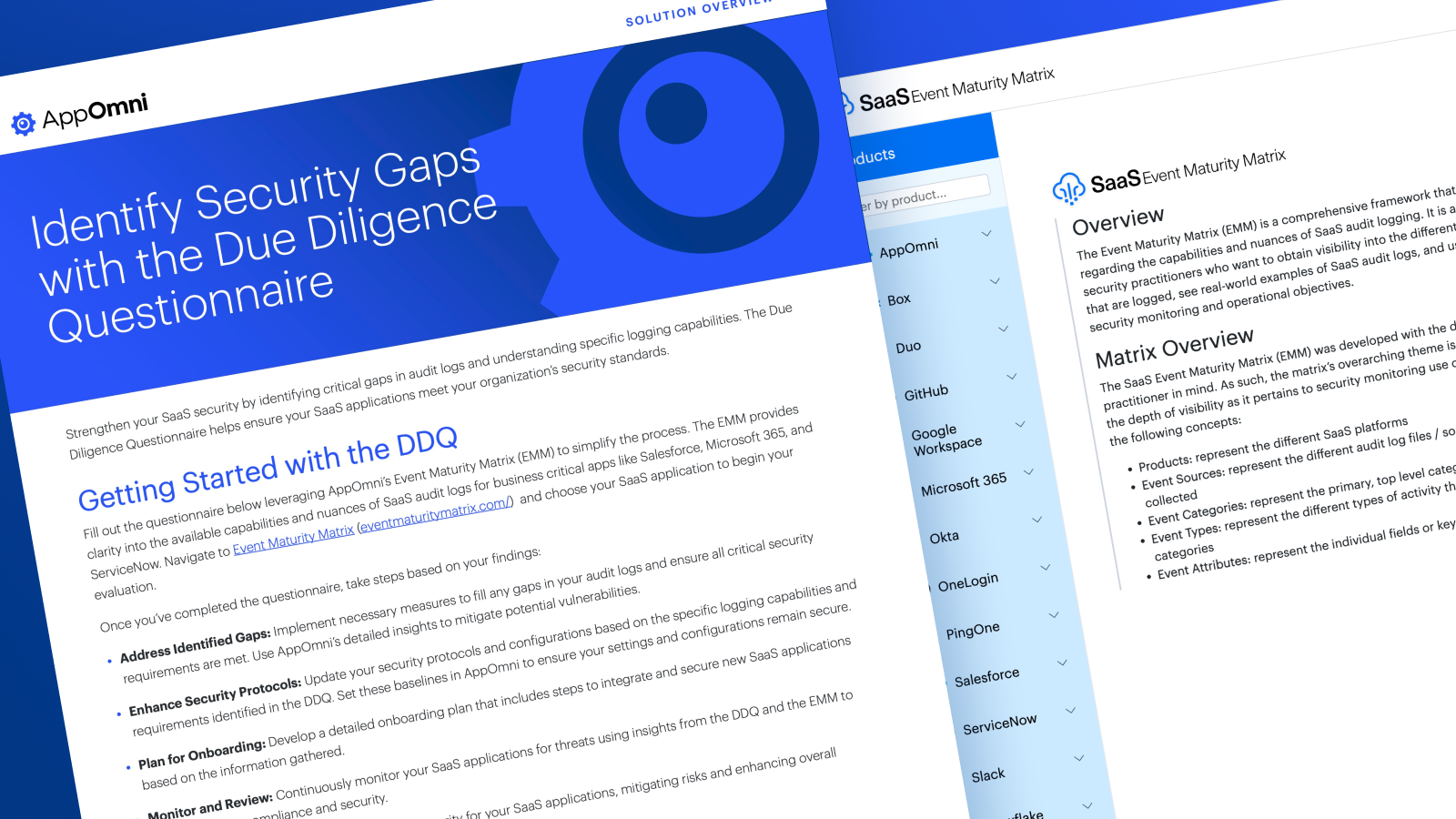
Use the DDQ to:
- Expose missing SaaS audit events and logging gaps that impact detection and response
- Validate audit log access and SIEM integration to centralize SaaS visibility
- Set secure logging baselines and onboarding standards for new SaaS applications
Centralized Log Streaming and SIEM Integration
SaaS visibility starts with knowing whether audit logs can reach your SIEM tools.
Key questions to answer:
- Real-time or batch delivery: Can events be streamed or pushed to SIEM tools such as Splunk or Google Chronicle in near real time, or only via periodic exports?
- Customer access or vendor only: Are audit logs available to your team, or held internally and released only during an incident?
Without direct SIEM access, SaaS threats are harder to detect, investigate, and respond to in time.
Audit SaaS Data Accessibility and Retention
Visibility depends on how long audit logs are kept and how easily your team can access them.
Key questions to answer:
- API access: Can you automatically retrieve at least 90 days of audit activity?
- Log requests: If no API exists, is there a clear process to request logs for investigations or audits?
Limited access and short retention windows slow incident response and create compliance risk.


Turning Logs Into Actionable Defense
Closing the visibility gap is not just about collecting logs. It’s about putting them to work.
Once the DDQ highlights gaps, SecOps teams can:
- Eliminate SaaS logging blind spots with AppOmni’s SaaS-specific insights
- Set secure baselines for logging, configurations, and integrations
- Continuous security event monitoring for threats and misconfigurations
Together, the DDQ and Event Maturity Matrix help teams move from basic logging to SIEM-ready SaaS visibility. Audit data becomes an active defense tool instead of a last-resort artifact.
Download the DDQ ↑
More Interesting Guides
-

CSPM vs SSE/SASE vs CASB vs SSPM: Who Secures What
Learn how CSPM, SASE, CASB, and SSPM differ, and where each fits in securing cloud infrastructure, access, and SaaS applications. Discover the critical visibility gaps in modern security stacks.
-

The Top 3 Ways Criminals Use AI in Cyber Attacks
AI-driven SaaS security risks grow fast. Here’s what to watch out for and how to prevent breaches.
-

EvilToken and Microsoft 365: A Familiar Attack Playbook, Scaled with AI
High-value M365 user orgs targeted by an AI-powered device code phishing campaign. Here’s how the EvilToken attack happened, and what prevention controls to take.
